A hacker’s claim to have stolen more than 10 petabytes of sensitive information from China’s National Supercomputing Center (NSCC) in Tianjin has triggered alarm across cybersecurity circles, not only because of the sheer scale of the alleged breach, but because of what the dataset may contain. If the leak is genuine, it could amount to the largest known theft of data from China, exposing years of research linked to defense, aerospace, advanced science, and strategic technology programs.
What makes this case so striking is the profile of the target. The NSCC in Tianjin is not an ordinary computing facility. Opened in 2009 as China’s first national supercomputing center, it serves as a centralized infrastructure hub for around 6,000 clients, including research institutes, industrial users, and agencies tied to highly sensitive scientific and defense work. In practical terms, it is the kind of facility where large-scale simulations, advanced engineering tasks, and complex national-level research projects are processed. A breach here would not be just another cyber incident. It would represent a direct compromise of a strategic knowledge repository.

The alleged attacker, operating under the name FlamingChina, reportedly posted a sample of the dataset on an anonymous Telegram channel , claiming it included research from fields such as aerospace engineering, military research, bioinformatics, and fusion simulation. Experts who reviewed parts of the posted material said the samples appeared consistent with the kind of data one would expect from a supercomputing center serving high-level institutions. Among the files reportedly seen were documents marked “secret” in Chinese, login credentials, internal folders, technical manuals, missile-related schematics, animated simulations, and renderings linked to weapons testing and aerospace systems.
The names allegedly connected to the leaked data make the matter even more serious. According to the claims, the material is linked to major Chinese organizations such as the Aviation Industry Corporation of China (AVIC), the Commercial Aircraft Corporation of China (COMAC), and the National University of Defense Technology. Whether every one of those links can be verified remains uncertain, but even partial authenticity would raise major concerns. These are not minor institutions; they sit at the heart of China’s military-industrial and technological modernization efforts.
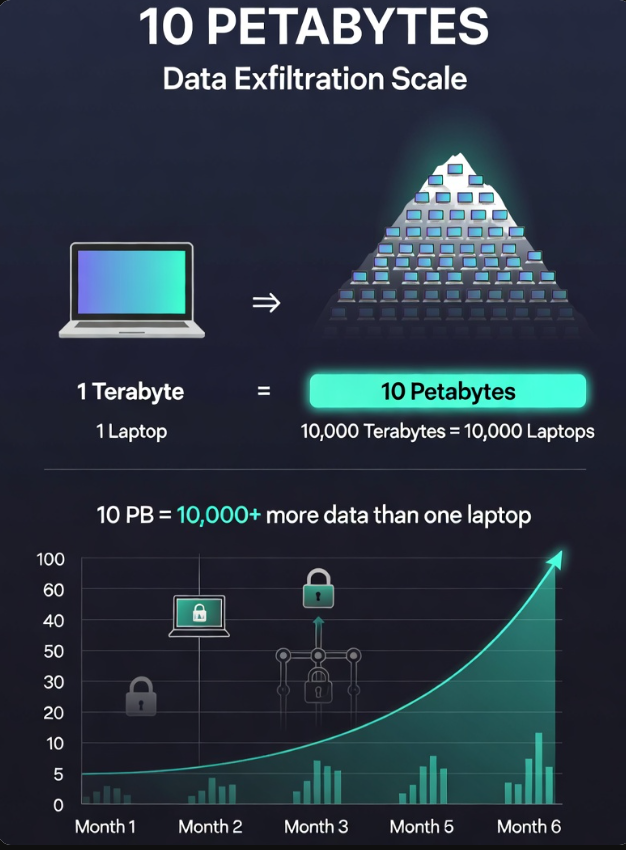
The scale alone is difficult to grasp. One petabyte equals 1,000 terabytes, and a high-end personal laptop typically stores about one terabyte. That means the alleged haul of more than 10 petabytes would be equivalent to the contents of roughly 10,000 high-spec laptops. This is not simply a folder of classified files. It is a data mountain large enough to contain years of research, testing records, simulations, design models, and supporting documentation. For intelligence services, the value would not lie only in individual documents, but in patterns, trends, and long-term insight into China’s priorities, capabilities, and technical bottlenecks.
According to accounts shared by researchers who contacted the alleged hacker, access may have been gained through a compromised VPN domain. Once inside, the attacker reportedly deployed a botnet to distribute the extraction process across multiple systems. Instead of moving huge volumes of information through one obvious channel, the data was allegedly siphoned out gradually over about six months, with smaller packets moving across different nodes. That method matters because it reduces the chance of triggering alarms. Security teams are far more likely to notice a massive transfer to a single destination than small, distributed flows spread over time.
What stands out in expert commentary is that the method was not described as exceptionally revolutionary. In fact, some analysts suggested the attack’s effectiveness may have come less from extraordinary sophistication and more from weaknesses in system architecture and monitoring. That possibility is perhaps the most damaging aspect of the story. If a strategic computing hub could be penetrated and drained slowly over months without detection, it would suggest not just a single failure, but a structural problem in oversight, segmentation, and response capability.
This is where the alleged breach becomes more than a technical story. It becomes a geopolitical one. If the stolen material includes real defense and aerospace research, it could offer China’s rivals rare visibility into covert programs, weapons testing pathways, simulation models, and research directions. Information of that scale and complexity would likely be most useful not to ordinary cybercriminals, but to state intelligence services with the manpower, computing resources, and analytical capability to process it. In other words, the real value of the data may not be immediate publication, but strategic exploitation.
The breach also cuts into a core Chinese policy ambition: technological self-reliance. Beijing has invested heavily in supercomputing and indigenous infrastructure partly to reduce dependence on Western technology, especially amid tightening export controls on advanced chips. But secure infrastructure is not defined only by who builds it. It is also defined by whether it can be defended. If one of China’s flagship supercomputing hubs has indeed been compromised on this scale, the incident would expose a sharp contradiction between technological ambition and cybersecurity resilience.
There is also important historical context. China has faced major data security scandals before. In 2021, a huge database containing personal information on up to one billion Chinese citizens was reportedly left exposed for more than a year before wider attention followed in 2022. That earlier case showed how damaging weak cyber hygiene can be at national scale. The alleged Tianjin breach, however, would be even more serious because the focus here is not consumer data but strategic research and possible military information.
China’s own policymakers have already acknowledged that cybersecurity remains a weak point. The country’s 2025 National Security White Paper called for stronger protection of network, data, and AI systems, recognizing the need for more robust defenses around key information infrastructure. That language now feels especially relevant. If the Tianjin case is confirmed, it will not just be an embarrassment. It will be a warning that in the race for scientific and military advantage, the greatest vulnerability may not lie in chips or hardware shortages, but in the unseen gaps inside the systems themselves.
The Tianjin story remains an alleged breach, not a fully verified one. Chinese authorities have not confirmed it, and some claims still require independent validation. Yet even at this stage, the case has already become significant. It reveals how modern power is stored not only in weapons or factories, but in data, models, simulations, and research archives. And it shows that in the age of cyber conflict, losing control of information may be as consequential as losing control of territory.











Leave a Reply